What Is a Proxy vs VPN: Which One Should You Use?
Eneba Hub contains affiliate links, which means we may earn a small commission if you make a purchase through them—at no extra cost to you. Learn more
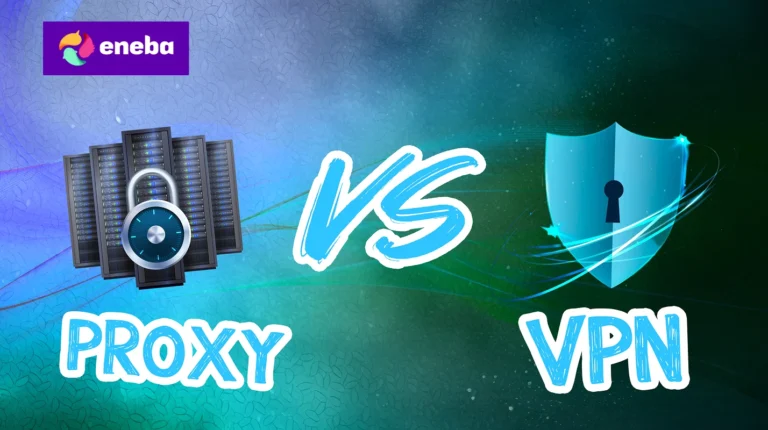
Understanding what is a proxy vs VPN comes down to one fundamental question: do you want to hide your location or protect your entire connection? Both tools mask your IP address, but that’s where the similarities end. After years of testing both for gaming, streaming, and general privacy, I’ve learned when each option makes sense and when you’re wasting your time with the wrong tool.
Keep reading to learn exactly how these tools work and when I use each one.
Jump to:
Quick Comparison: Proxy vs VPN
| Feature | Proxy | VPN |
|---|---|---|
| Encryption | None (most proxies) | Full traffic encryption (AES-256) |
| IP Masking | Yes | Yes |
| Speed Impact | Minimal (5-10% loss) | Moderate (10-20% loss) |
| Coverage | Single app or browser | Entire device/system |
| Privacy Protection | Low | High |
| ISP Visibility | Can see your traffic | Can’t see your traffic |
| Setup Complexity | Per-application | System-wide with one click |
| Cost | Often free | $2-15/month |
| Best For | Quick geo-bypassing, scraping | Privacy, security, torrenting |
What Is a Proxy Server?

A proxy server acts as an intermediary between your device and the websites you visit. Instead of connecting directly to a site, your request goes to the proxy first. The proxy then forwards your request using its own IP address, making it appear that the connection originates from the proxy’s location rather than yours.
Think of it like asking a friend to buy something for you. The store sees your friend, not you. But your friend isn’t encrypting your shopping list or hiding what you’re purchasing. They’re just making the transaction on your behalf.
How proxies work technically
When you configure a proxy, you’re telling a specific application (usually your browser) to route traffic through an intermediary server. Your browser sends requests to the proxy, which strips your IP address and replaces it with its own before forwarding the request to the destination website. The response travels back through the same path.
This happens at the application level only. Your operating system, other browsers, games, and background applications continue connecting directly to the internet using your real IP address. This limited scope is both a feature and a limitation, depending on your use case.
Types of proxy servers
HTTP proxies handle standard web traffic. They work with browsers and applications that use HTTP/HTTPS protocols. Most free proxies fall into this category. They’re functional for basic browsing but don’t support other traffic types like gaming or video calls.
SOCKS proxies operate at a lower level, handling any type of traffic including HTTP, FTP, and P2P connections. SOCKS5 is the current standard and includes authentication support. Torrent users sometimes prefer SOCKS5 proxies because they work with P2P clients while adding minimal speed overhead. NordVPN actually includes SOCKS5 proxy access alongside its VPN service, which I find useful for specific torrenting setups.
Transparent proxies don’t hide that you’re using a proxy. Organizations use them for content filtering and caching. You’ve probably connected through corporate or school transparent proxies without knowing it.
Residential proxies use IP addresses assigned to real homes by ISPs, making them appear as regular user connections. These are popular for web scraping and accessing services that block datacenter IPs. They’re also significantly more expensive than standard proxies.
What proxies don’t do
Proxies don’t encrypt your traffic. Your ISP can still see everything you’re doing online. The websites you visit can still track your behavior through cookies, browser fingerprinting, and other methods. The proxy operator can see all your unencrypted traffic.
Most proxies don’t protect against DNS leaks either. Even with a proxy configured, your DNS requests might still go through your ISP’s servers, revealing which websites you’re visiting despite the IP masking.
What Is a VPN?

A Virtual Private Network creates an encrypted tunnel between your device and a VPN server. All your internet traffic travels through this tunnel, invisible to anyone watching your connection. The VPN server then connects to websites on your behalf, masking your IP address just like a proxy, but with the added layer of encryption, which protects everything in transit.
The difference is fundamental. A proxy is a relay. A VPN is a secure, encrypted tunnel that hides not just your destination but everything about your connection.
How VPNs work technically
When you connect to a VPN, client software on your device establishes an encrypted connection to a VPN server. This encryption typically uses the AES-256 cipher, the same standard governments use for classified information. Your device encrypts all outgoing traffic before it leaves, and the VPN server decrypts it before forwarding to the destination.
This happens at the system level. Every application on your device routes through the VPN tunnel automatically. Your browser, games, streaming apps, torrent clients, and background services all use the encrypted connection. Nothing leaks through your regular internet connection.
VPNs encrypt your traffic through the so-called connection protocols. If you want to learn more about traffic encryption, check my full guide on the best VPNs for encrypted internet connection.
VPN protocols explained
WireGuard is the current performance leader. It uses modern cryptography, maintains smaller codebases, and connects almost instantly. Most speed-focused VPNs now offer WireGuard or proprietary variants built on it. It’s the best VPN protocol for gaming and other speed-dependent activities.
OpenVPN is the established standard with decades of security audits. It’s slower than WireGuard but extremely reliable and widely supported. When compatibility matters more than speed, OpenVPN works almost everywhere.
IKEv2/IPSec handles connection switching well, so it’s popular for mobile devices. When you switch between Wi-Fi and cellular, IKEv2 reconnects faster than other protocols.
We have some older protocols like PPTp, which are no longer considered safe, and I strongly recommend against using them.
What VPNs provide that proxies don’t
Full traffic encryption means your ISP sees only that you’re connected to a VPN server. They can’t see which websites you visit, what you download, or what services you use. This matters for privacy-conscious users and anyone dealing with ISP throttling.
Kill switches prevent traffic leaks if the VPN connection drops. Without a kill switch, a momentary disconnection could expose your real IP address. Quality VPNs halt all internet traffic until the secure connection re-establishes.
DNS leak protection ensures your DNS requests route through the VPN tunnel rather than your ISP’s servers. This closes a common privacy gap that proxies typically ignore.
System-wide coverage protects everything automatically. You don’t need to configure each application individually or worry about which programs are exposed.
Proxy vs VPN: Security Comparison

Security is where VPNs decisively win. This isn’t subjective; it’s a matter of what these tools fundamentally do.
Encryption difference
Proxies transmit your data in plaintext. Anyone monitoring your network connection, whether your ISP, a hacker on public Wi-Fi, or a government agency, can see exactly what you’re doing. The proxy hides your IP from the destination website, but everything between you and the proxy is exposed.
VPNs scramble all traffic with military-grade encryption. Even if someone intercepts your data, they see meaningless encrypted packets. Breaking AES-256 encryption with current technology would take longer than the age of the universe.
Trust requirements
Both proxies and VPNs require trusting the operator. The proxy or VPN server sees your unencrypted traffic (or can decrypt it for VPNs). This is why choosing reputable providers matters.
The difference is accountability. Free proxies have no business model besides selling your data or injecting ads. VPN providers with paid subscriptions, independent audits, and verified no-logs policies have reputation and legal consequences for violating trust. The best VPNs on the market undergo regular third-party audits proving their privacy claims.
Public Wi-Fi scenarios
On public Wi-Fi, proxies provide almost no security benefit. Your traffic travels unencrypted to the proxy server, meaning anyone on the same network can intercept it. Coffee shop hackers, malicious hotspots, and network sniffers all see your data clearly.
VPNs encrypt traffic before it leaves your device. Public Wi-Fi security becomes irrelevant because attackers only see encrypted packets traveling to the VPN server. I never connect to public Wi-Fi without a VPN active, even for basic browsing.
Proxy vs VPN: Speed and Performance

Speed is where proxies have a legitimate advantage, though modern VPNs have narrowed the gap significantly.
Why proxies are faster
No encryption means no processing overhead. Your device doesn’t need to encrypt outgoing traffic or decrypt incoming data. The proxy simply relays packets without transformation.
Proxies also typically connect faster. There’s no handshake protocol, key exchange, or tunnel establishment. You configure the proxy address, and traffic routes through it immediately.
For bandwidth-intensive tasks that don’t require security, proxies deliver near-native speeds. Web scraping operations, for example, often use proxy pools because the speed advantage matters at scale, and the data being collected is public anyway.
VPN speed realities
Modern VPN protocols have minimized the encryption overhead. WireGuard-based connections typically show 10-20% speed reduction on local servers, sometimes less. On a 500 Mbps connection, you might see 400-450 Mbps through a quality VPN. That’s fast enough for any consumer use case including 4K streaming and large downloads.
The fastest VPNs for gaming add minimal latency. I regularly game through VPN connections without noticing performance differences. The encryption overhead is measured in milliseconds, not seconds.
Distance matters more than encryption. Connecting to a VPN server across the globe introduces latency from physical distance regardless of protocol efficiency. Local servers perform nearly as well as direct connections.
When speed differences matter
For competitive gaming where single-digit milliseconds matter, proxies theoretically have an edge. In practice, I’ve found that quality VPN servers in my region perform identically to direct connections for gaming purposes.
For bulk operations like web scraping thousands of pages, proxy speed advantages compound. Saving 5% per request across millions of requests adds up to significant time and resource savings.
For normal browsing, streaming, and gaming, VPN speeds are indistinguishable from direct connections on quality providers. The security benefits far outweigh the marginal speed cost.
When to Use a Proxy

Despite preferring VPNs for most situations, I use proxies for specific tasks where their characteristics provide genuine advantages.
Web scraping and automation
When collecting publicly available data at scale, proxies make sense. You need IP rotation to avoid rate limits, not encryption. Residential proxy pools cycle through thousands of IP addresses, making automated requests appear as organic traffic from different users. Encrypting this traffic would add overhead without security benefits since the data is public anyway.
Quick geo-checks
Sometimes I just need to verify how a website appears from a different country. Browser proxy extensions let me switch locations in seconds without connecting a full VPN. For a quick check that doesn’t involve sensitive data, this convenience matters.
Testing and development
When testing applications that need to see different geographic behavior, proxies provide faster iteration than VPN connections. Configure a proxy, test, switch to another, test again. No connection delays, no client software to manage.
Bandwidth-critical operations
Some operations genuinely can’t tolerate any speed reduction. Professional streamers, for example, sometimes use SOCKS5 proxies to mask their IP while minimizing latency impact on their broadcasts. The encryption overhead of VPNs, while small, can matter when you’re pushing maximum upload bandwidth.
When to Use a VPN

For almost everything else, I use a VPN. The security benefits justify the minimal speed cost.
All sensitive browsing
Banking, shopping, email, anything involving personal information goes through my VPN. The encryption ensures nobody between me and the destination can see what I’m doing. This isn’t paranoia; it’s basic security hygiene.
Torrenting and P2P
VPNs are essential for torrenting. Proxies don’t encrypt traffic, meaning your ISP sees exactly what you’re downloading. Copyright enforcement agencies monitor P2P swarms and connect IP addresses to downloads. A VPN hides both your activity from your ISP and your IP address from other peers.
Quality VPNs also offer kill switches that halt torrent traffic if the connection drops, preventing accidental IP exposure. Some include SOCKS5 proxies specifically for torrent clients, giving you both options. Learning how to use a VPN on PC takes minutes and protects all your P2P activity.
Gaming protection
DDoS attacks target gamers, especially streamers and competitive players. A VPN masks your real IP address, preventing attackers from directing traffic at your connection. The best VPNs for gaming provide DDoS protection while adding minimal latency.
I also use VPNs to access game servers in different regions for off-peak matchmaking or to play with friends in other countries. The encrypted connection ensures my ISP can’t throttle gaming traffic.
Streaming geo-restricted content
Streaming services actively detect and block proxies. They maintain databases of known proxy IP addresses and deny access. VPNs, especially those with regularly refreshed IP pools and obfuscation features, successfully access geo-restricted content that proxies can’t reach.
The best VPNs for streaming work reliably with major platforms. I’ve never had consistent success with proxies for streaming purposes.
Public and untrusted networks
Hotels, airports, coffee shops, conferences, anywhere with public Wi-Fi demands VPN protection. I don’t make exceptions. The five seconds to connect is worth the complete protection against network-based attacks.
Bypassing ISP throttling:
ISPs throttle specific types of traffic, particularly streaming and gaming during peak hours. Since they can’t identify traffic through an encrypted VPN tunnel, throttling becomes impossible. If your connection seems slow only for certain activities, a VPN often restores full speeds.
My Personal Preferences and Setup
After testing dozens of both proxies and VPNs, here’s my actual setup for different use cases:
- Daily browsing: VPN always active. I use NordVPN, Surfshark, or ExpressVPN depending on what I need. The system-wide protection means I never accidentally browse unprotected.
- Gaming sessions: VPN connected to a local server with WireGuard protocol. The latency impact is undetectable, and I’m protected from DDoS attacks and IP exposure. For competitive games where I want absolutely minimal latency, I’ll occasionally game without VPN on trusted home networks, but never on streams where my IP could be grabbed.
- Torrenting: Always VPN with kill switch enabled. No exceptions. The speed overhead is negligible, and the protection is essential. I configure my torrent client to only connect when the VPN is active.
- Web scraping projects: Proxy pools for public data collection. Residential proxies when the target site blocks datacenter IPs. No need for encryption when collecting publicly accessible information at scale.
- Quick location checks: Browser proxy extension for 30-second tests. If I need more than a quick peek, I switch to the VPN.
- Public Wi-Fi: VPN before connecting to anything else. I’ve made this automatic through the VPN client settings. The moment I join an unknown network, the VPN activates.
The pattern is clear: VPN for anything involving my actual data, accounts, or privacy. Proxy for specific technical tasks where speed matters and security doesn’t. If you’re looking for a great VPN , all the top options are listed in my full guide on the best VPNs for this year.
FAQs
Yes. Traffic flows through your VPN tunnel first, then through the proxy. This adds another layer of IP masking but also adds complexity and latency. Most users don’t need this setup.
Generally no. Most free proxy operators monetize by logging traffic, injecting ads, or selling your data. If you need a proxy, paid services from reputable providers are worth the cost.
Yes, to an extent. Quality VPNs reduce speeds by 10-20% on local servers, often less. For most connections, this is imperceptible. Budget or overloaded VPNs can slow connections significantly more.
Yes, your ISP can see that you’re connecting to a proxy or VPN server. With proxies, they can also see your traffic content. With VPNs, they see only encrypted data traveling to the VPN server and can’t determine what you’re doing.
No. Proxies don’t encrypt traffic, so anyone on the same network can intercept your data. Only VPNs provide public Wi-Fi protection.